|
1 | 1 | --- |
2 | 2 | title: Setting the BitLocker encryption algorithm for Autopilot devices |
3 | 3 | description: Microsoft Intune provides a comprehensive set of configuration options to manage BitLocker on Windows devices. |
4 | | -keywords: Autopilot, BitLocker, encryption, 256-bit, Windows 10 |
5 | 4 | ms.prod: w10 |
6 | | -ms.mktglfcycl: deploy |
7 | | -ms.sitesec: library |
8 | | -ms.pagetype: deploy |
9 | 5 | ms.localizationpriority: medium |
10 | | -audience: itpro |
11 | 6 | author: aczechowski |
12 | 7 | ms.author: aaroncz |
13 | 8 | ms.reviewer: jubaptis |
14 | 9 | manager: dougeby |
15 | | -ms.date: 12/16/2020 |
| 10 | +ms.date: 06/15/2022 |
16 | 11 | ms.collection: M365-modern-desktop |
17 | 12 | ms.topic: how-to |
18 | 13 | --- |
19 | 14 |
|
20 | | - |
21 | 15 | # Setting the BitLocker encryption algorithm for Autopilot devices |
22 | 16 |
|
23 | 17 | **Applies to** |
24 | 18 |
|
25 | 19 | - Windows 11 |
26 | 20 | - Windows 10 |
27 | 21 |
|
28 | | -BitLocker [automatically encrypts](/windows-hardware/design/device-experiences/oem-bitlocker#bitlocker-automatic-device-encryption) internal drives during the Out Of Box Experience (OOBE) for devices that support [Modern Standby](/windows-hardware/design/device-experiences/modern-standby) or meet the [Hardware Security Testability Specification (HSTI)](/windows-hardware/test/hlk/testref/hardware-security-testability-specification). By default, BitLocker uses XTS-AES 128-bit used space only for automatic encryption. |
| 22 | +BitLocker [automatically encrypts](/windows-hardware/design/device-experiences/oem-bitlocker#bitlocker-automatic-device-encryption) internal drives during the out of box experience (OOBE) for devices that support [Modern Standby](/windows-hardware/design/device-experiences/modern-standby) or meet the [Hardware Security Testability Specification (HSTI)](/windows-hardware/test/hlk/testref/hardware-security-testability-specification). By default, BitLocker uses XTS-AES 128-bit used space only for automatic encryption. |
| 23 | + |
| 24 | +With Windows Autopilot, you can configure BitLocker encryption settings to apply before automatic encryption starts. This configuration makes sure the default encryption algorithm or type isn't applied automatically. A device that receives these settings after encrypting automatically will need to be decrypted before changing the encryption algorithm. |
29 | 25 |
|
30 | | -With Windows Autopilot, you can configure BitLocker encryption settings to get applied before automatic encryption starts. This configuration makes sure the default encryption algorithm or type isn't applied automatically. A device that recieves these settings after encrypting automatically will need to be decrypted before changing the encryption algorithm. |
| 26 | +## Encryption algorithm |
31 | 27 |
|
32 | | -## <span id="Encryption_algorithm"></span>Encryption algorithm |
| 28 | +The BitLocker encryption algorithm is used when BitLocker is first enabled. During Autopilot, BitLocker will be enabled after the device setup portion of the [enrollment status page](enrollment-status.md). The following encryption algorithms are available: |
33 | 29 |
|
34 | | -The BitLocker encryption algorithm is used when BitLocker is first enabled. During Autopilot, BitLocker will be enabled after the Device setup portion of the [Enrollment Status Page](enrollment-status.md) (ESP). Available encryption algorithms are: AES-CBC 128-bit, AES-CBC 256-bit, XTS-AES 128-bit, or XTS-AES 256-bit encryption. The default value is XTS-AES 128-bit encryption. See [BitLocker CSP](/windows/client-management/mdm/bitlocker-csp) for information about the recommended encryption algorithms to use. |
| 30 | +- AES-CBC 128-bit |
| 31 | +- AES-CBC 256-bit |
| 32 | +- XTS-AES 128-bit (default) |
| 33 | +- XTS-AES 256-bit |
| 34 | + |
| 35 | +For more information about the recommended encryption algorithms to use, see [BitLocker CSP](/windows/client-management/mdm/bitlocker-csp). |
35 | 36 |
|
36 | 37 | To make sure the BitLocker encryption algorithm you want is set before automatic encryption occurs for Autopilot devices: |
37 | 38 |
|
38 | | -1. Configure the [encryption method settings](../intune/protect/encrypt-devices#create-an-endpoint-security-policy-for-bitlocker) in the Endpoint Security disk encryption policy. The settings are available under **Endpoint Security** > **Disk encryption** > **Create policy** > **Platform** = Windows 10 and later, **Profile type** = BitLocker. |
| 39 | +1. Configure the [encryption method settings](../intune/protect/encrypt-devices.md#create-an-endpoint-security-policy-for-bitlocker) in the Endpoint Security disk encryption policy. The settings are available under **Endpoint Security** > **Disk encryption** > **Create policy** > **Platform** = Windows 10 and later, **Profile type** = BitLocker. |
| 40 | + |
39 | 41 | 2. [Assign the policy](../intune/configuration/device-profile-assign.md) to your Autopilot device group. The encryption policy must be assigned to **devices** in the group, not users. |
40 | | -3. Enable the Autopilot [Enrollment Status Page](enrollment-status.md) (ESP) for these devices. If the ESP isn't enabled, the policy won't apply before encryption starts. |
41 | 42 |
|
42 | | -An example of Endpoint Security disk encryption settings is shown below. |
| 43 | +3. Enable the Autopilot [enrollment status page](enrollment-status.md) for these devices. If you don't enable this feature, the policy won't apply before encryption starts. |
43 | 44 |
|
44 | | -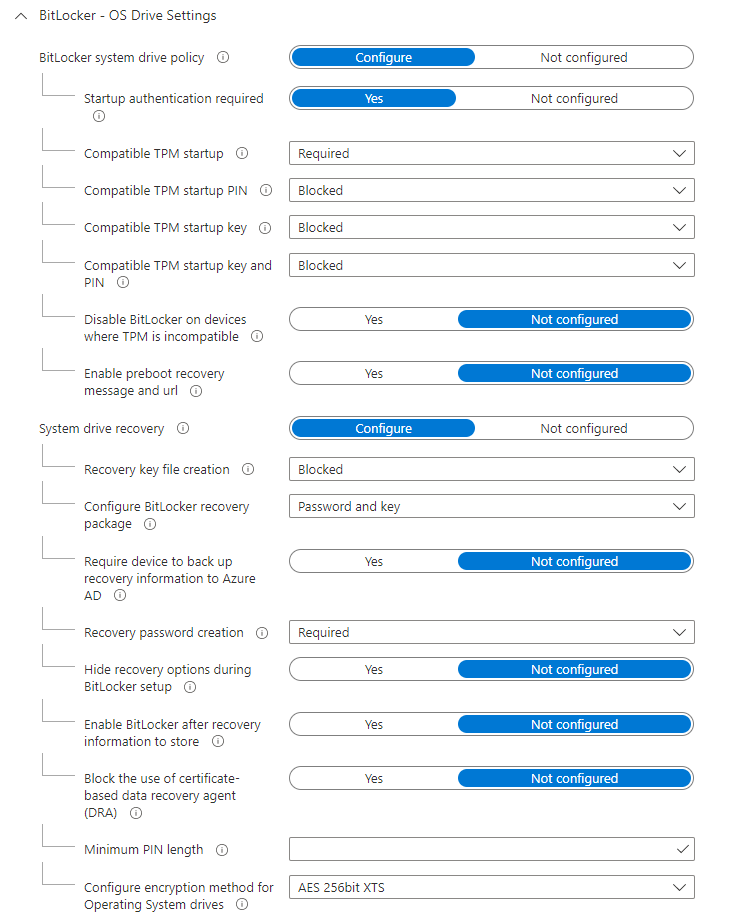 |
| 45 | +The following image is an example of the Endpoint Security disk encryption settings. |
45 | 46 |
|
46 | | -## <span id="Full_disk_vs_Used_Space_only_encryption"></span>Full disk vs Used Space only encryption |
| 47 | +:::image type="content" source="media/bitlocker/endpoint-security-disk-encryption-policy.png" alt-text="Screenshot example of the Endpoint Security disk encryption settings."::: |
47 | 48 |
|
48 | | -The type of drive encryption (full disk or used space only) is automatically determined by configuration of [silent enablement](/mem/intune/protect/encrypt-devices#silently-enable-bitlocker-on-devices) and hardware support for modern standby, but can be enforced by configuring the [SystemDrivesEncryptionType](/windows/client-management/mdm/bitlocker-csp) setting. Like the encryption algorithm, the encryption type is used when BitLocker is first enabled. See [Manage BitLocker policy](/mem/intune/protect/encrypt-devices#full-disk-vs-used-space-only-encryption) for information on expected encryption type behavior. |
| 49 | +## Full disk or used space-only encryption |
| 50 | + |
| 51 | +There are two types of encryption, full disk or used space-only. The type of encryption is automatically determined by configuration of [silent enablement](../intune/protect/encrypt-devices.md#silently-enable-bitlocker-on-devices) and hardware support for modern standby. You can enforce it by configuring the [SystemDrivesEncryptionType](/windows/client-management/mdm/bitlocker-csp) setting. Like the encryption algorithm, the encryption type is used when BitLocker is first enabled. For more information on the expected encryption type behavior, see [Manage BitLocker policy](../intune/protect/encrypt-devices.md#full-disk-vs-used-space-only-encryption). |
49 | 52 |
|
50 | 53 | To enforce the type of drive encryption used: |
51 | 54 |
|
52 | | -1. Configure the 'Enforce drive encryption type on operating system drives' setting within the [settings catalog](/mem/intune/configuration/settings-catalog). This setting is available in the **Administrative Templates > Windows Components > BitLocker Drive Encryption > Operating System Drives** category from the settings picker. |
| 55 | +1. Configure the **Enforce drive encryption type on operating system drives** setting within the [settings catalog](../intune/configuration/settings-catalog.md). This setting is available in the **Administrative Templates > Windows Components > BitLocker Drive Encryption > Operating System Drives** category from the settings picker. |
| 56 | + |
53 | 57 | 2. [Assign the policy](../intune/configuration/device-profile-assign.md) to your Autopilot device group. The encryption policy must be assigned to **devices** in the group, not users. |
54 | | -3. Enable the Autopilot [Enrollment Status Page](enrollment-status.md) (ESP) for these devices. If the ESP isn't enabled, the policy won't apply before encryption starts. |
55 | 58 |
|
56 | | -An example of the settings catalog profile is shown below. |
| 59 | +3. Enable the Autopilot [enrollment status page](enrollment-status.md) for these devices. If you don't enable this feature, the policy won't apply before encryption starts. |
57 | 60 |
|
58 | | -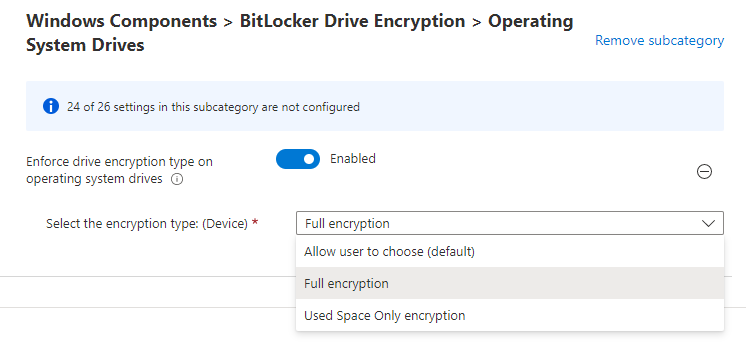 |
| 61 | +The following image is an example of the settings catalog profile. |
59 | 62 |
|
| 63 | +:::image type="content" source="media/bitlocker/settings-catalog-drive-type.png" alt-text="Screenshot example of the BitLocker drive type configuration in the settings catalog."::: |
60 | 64 |
|
61 | 65 | ## Requirements |
62 | 66 |
|
63 | | -Windows 10, version 1809 or later. |
| 67 | +A supported version of Windows 11 or Windows 10. |
64 | 68 |
|
65 | 69 | ## Next steps |
66 | 70 |
|
67 | 71 | [BitLocker overview](/windows/security/information-protection/bitlocker/bitlocker-overview) |
68 | | -[Manage BitLocker policy for Windows devices with Intune](/mem/intune/protect/encrypt-devices) |
| 72 | + |
| 73 | +[Manage BitLocker policy for Windows devices with Intune](../intune/protect/encrypt-devices.md) |
0 commit comments